LDAP connector
The LDAP connector can be used with any directory which supports the LDAP and LDAPS protocols such as OpenLDAP, Active Directory or eDirectory.
Installing the connector
The steps below describe how to install and start the connector. Depending on whether you are using Kubernetes, Swarm or RPM, the instructions will vary.
RPM File
First, download jar file into /usr/local/openiam/connectors/bin and change owner to OpenIAM user.
wget https://download.openiam.com/release/enterprise/4.2.1.4/connectors/ldap-connector-rabbitmq.jarchown openiam:openiam /usr/local/openiam/connectors/bin/ldap-connector-rabbitmq.jar
Next, create a new .sh file for starting LDAP connector by running:
nano ldap_start.sh
Content of the file:
#!/bin/bash. /usr/local/openiam/env.confexport VAULT_CERTS="$HOME_DIR/vault/certs/"export JAVA_HOME="$HOME_DIR/jdk"export JAR_FILE="ldap-connector-rabbitmq"export JAVA_OPTS="-Xmx256m -Djdk.tls.client.protocols=TLSv1.2"su openiam -c "$JAVA_HOME/bin/java -Dlogging.level.root=ERROR -Dlogging.level.org.openiam=ERROR -Dconfpath=$HOME_DIR/ -Djavax.net.ssl.keyStorePassword=changeit -Djavax.net.ssl.trustStore=$HOME_DIR/conf/$JAR_FILE/ -jar $JAVA_OPTS $HOME_DIR/connectors/bin/$JAR_FILE.jar > $HOME_DIR/logs/$JAR_FILE.log&"
Make file executable by running:
chmod +x ldap_start.sh
To start the connector, use the following command:
./ldap_start.sh
Docker swarm
Kubernetes
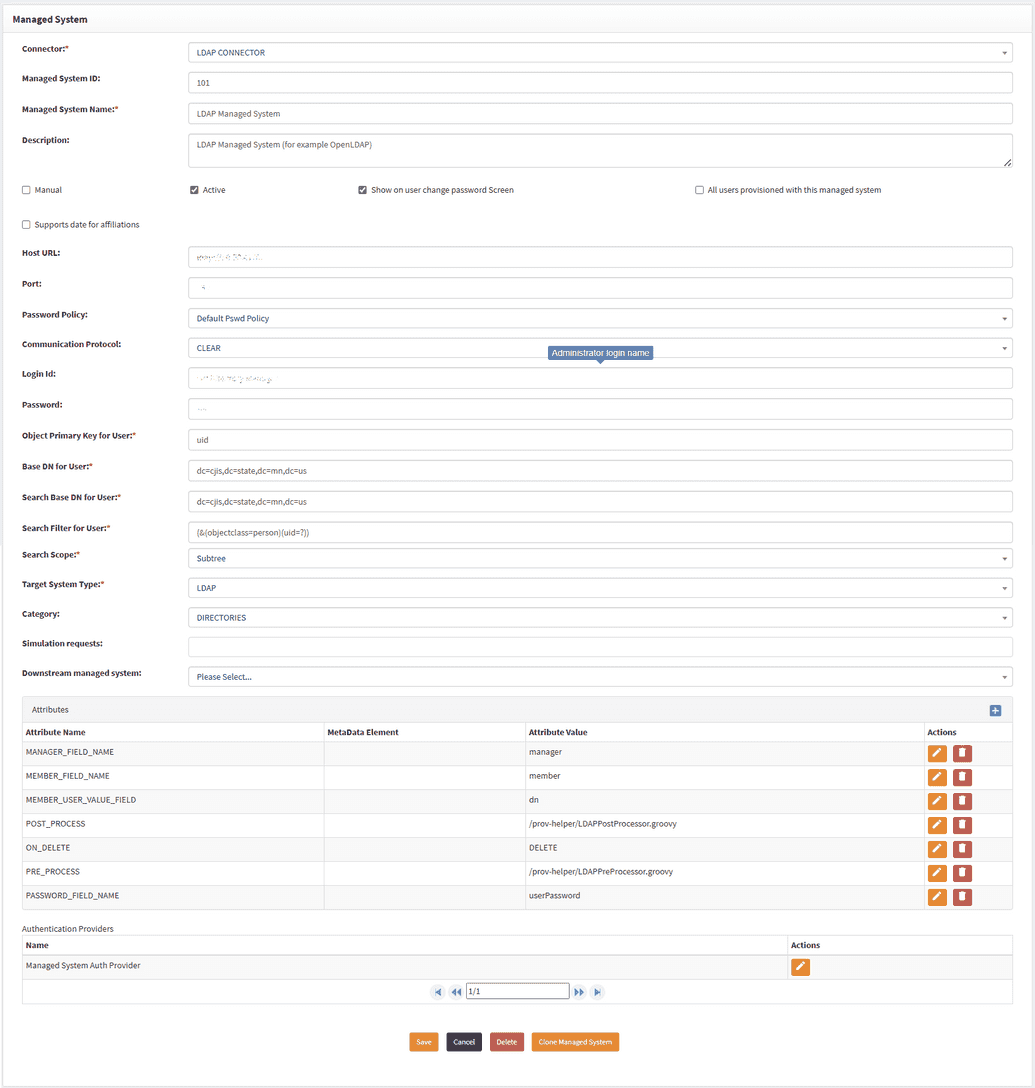
Configuring managed system
OpenIAM has an out-of-the-box Managed system configuration named OpenLDAP, which can be found by logging in to webconsole and going to Provisioning > Managed system. It can be used as is since it was mainly already configured. In the event one configures the managed system from scratch, the fields are to be filled manually.
Synchronization
OpenIAM provides two pre-configured synchronization options for LDAP connector:
- OpenLDAP User
- Matches users by
User ID.
- Matches users by
- OpenLDAP Group
- Matches groups by
nameandcn.
- Matches groups by
To access synchronization settings:
- Log in to the Web Console.
- Navigate to Provisioning > Synchronization.
- Search for
OpenLDAP UserorOpenLDAP Group.
Both synchronization configurations come with example transformation scripts.
Connector troubleshooting tips
SSL connection issue
Symptoms:
org.openiam.connector.core.base.exception.ConnectorException: javax.naming.CommunicationException: simple bind failed: xxxxx.xx.xxx.xxx.xxx:636 [Root exception is javax.net.ssl.SSLHandshakeException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target] Caused by: javax.naming.CommunicationException: simple bind failed: myldap.example.com:636
Solution:
- Make sure port is open and reachable, and you can connect via telnet command
telnet myldap.example.com 636
If you are connecting to LDAP via secured port 636 you should import ca_cert issued by domain into java keystore:
keytool -noprompt -import -v -trustcacerts -alias ldap_ca$(pwgen -s 13 1) -file /path/to/ca_cert.crt -keystore /usr/local/openiam/jdk/lib/security/cacerts -keypass changeit -storepass changeit