Managed System authentication
This section describes how to configure delegated authentication with an external Managed System.
Delegated authentication means that login and password for login into OpenIAM are not stored in OpenIAM database. Here, OpenIAM doesn't perform authentication itself, but passes login and password and then gets an approval/disapproval for authentication. One of the most frequently used Managed systems to authenticate are Active Directory or LDAP systems.
Configuring Managed System authentication
To configure Managed System or delegated authentication, follow the steps below.
- Define an authentication policy.
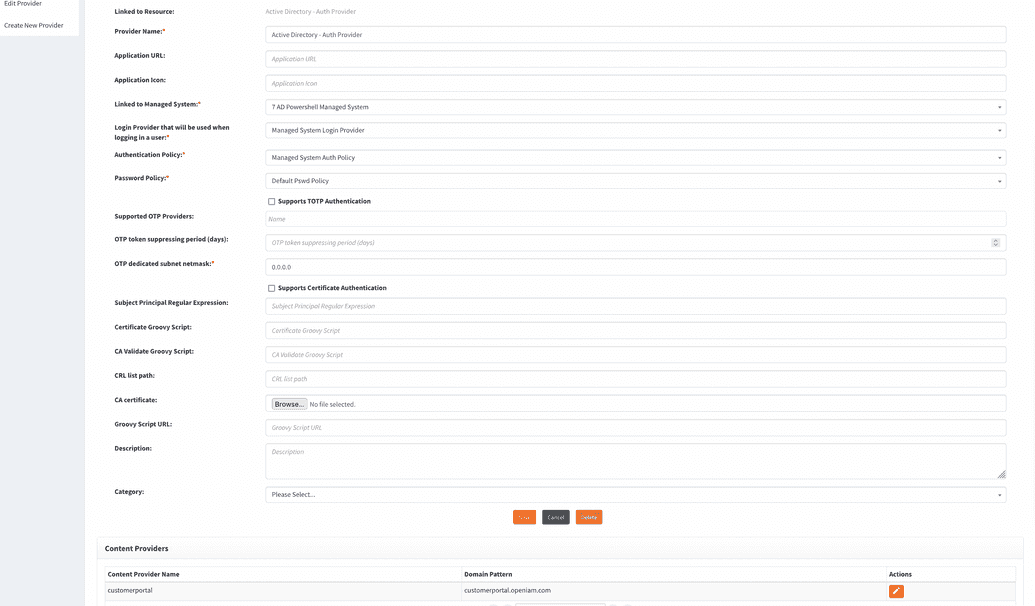
- Create an authentication provider (or use out-of-the-box configuration called Managed System Auth Provider, just select appropriate linked managed system. See a screenshot below).
- Link the authentication provider to a content provider.
Create an Authentication Provider
To create a new authentication provider, follow the steps below.
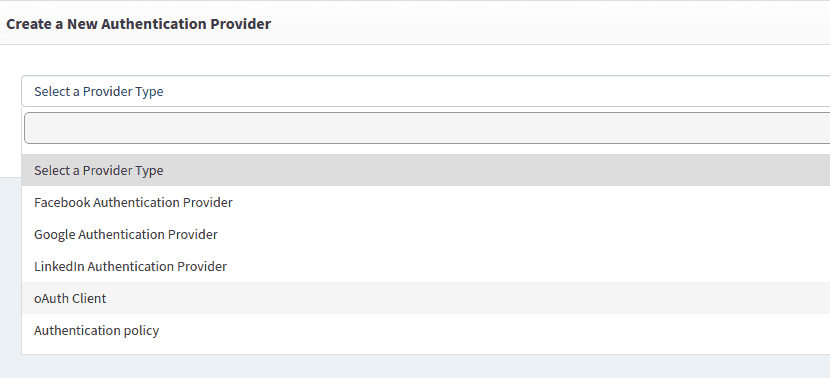
- Login to webconsole and go to Access Control > Authentication providers > Create new provider.
- From the dropdown shown in the image below, select Authentication policy.
For Managed System authentication provider type, it is vital for Managed System to be successfully connected to target system. Otherwise, authentication will fail. To check the Managed System connection, go to webconsole > Provisioning > Managed Systems dashboard.
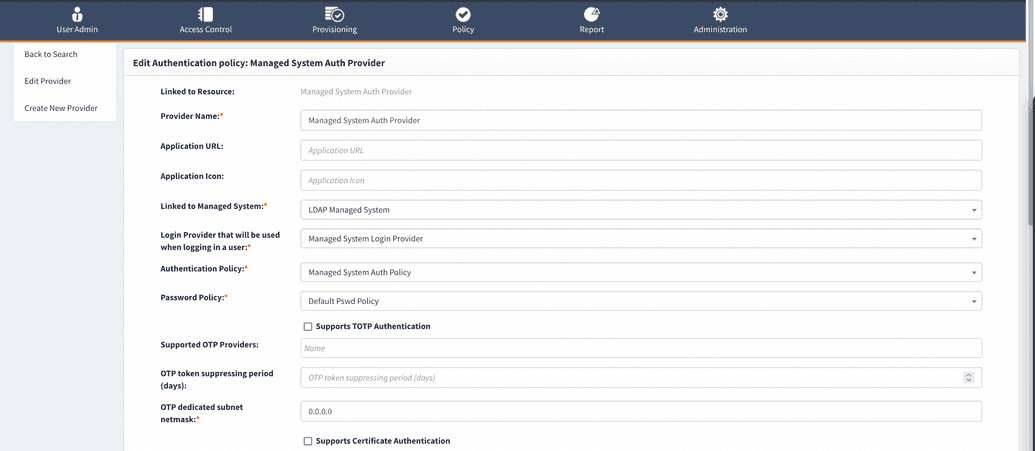
There are three fields in Authentication policy dashboard that are important for delegated authentication to work.
| Name | Required value |
|---|---|
| Linked to Managed system | In this field, choose a respective Managed System that provides login and password for authentication. |
| Login Provider that will be used when logging a user | To log in using specific Managed System, choose Managed System login provider. |
| Authentication policy | Choose the authentication policy created specifically for this Managed System. |
The required fields filling example are shown below.
Linking Authentication provider to a Content provider
After creating the Authentication provider, the next step is to associate it with a content provider. Follow the steps described below.
- Go to Access Control > Content providers.
- Select the Content provider that you want to update. In case there is only one, select the Default content provider.
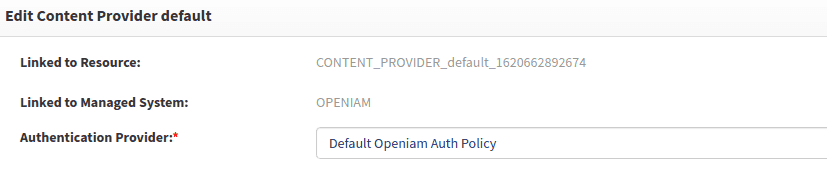
- Select the Authentication provider that you created earlier from the Authentication provider dropdown as shown in the example below.
- Save the configuration after making changes.
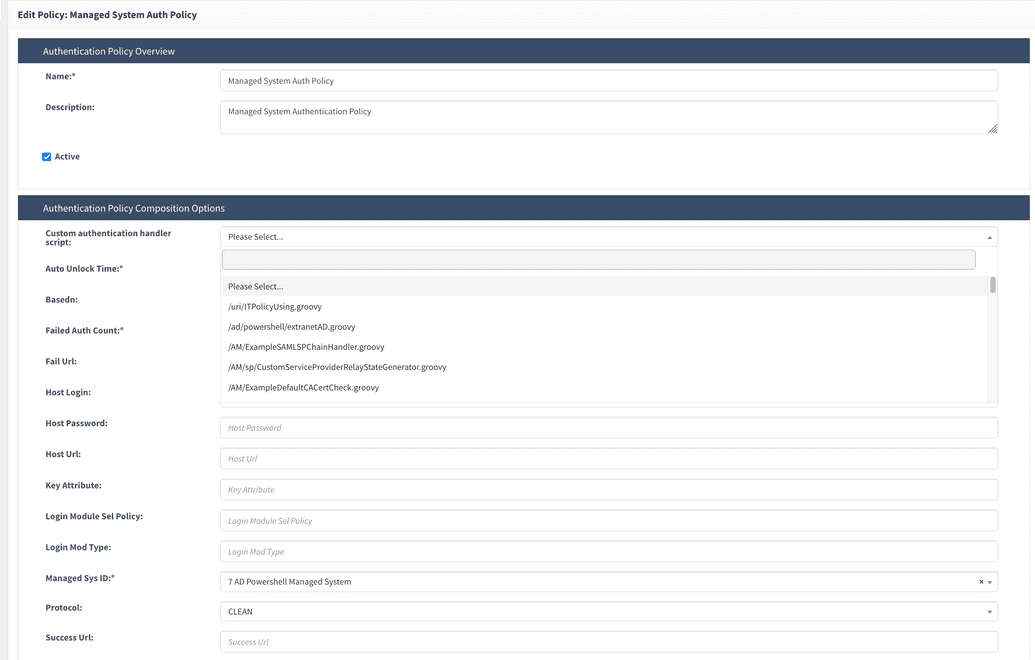
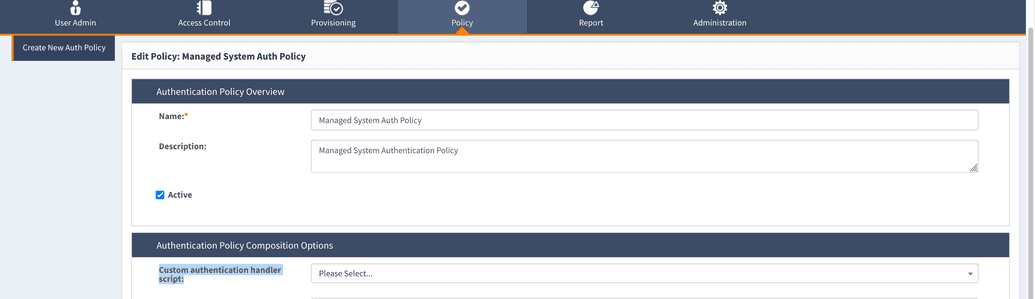
In case you need to tweak(change) principal somehow before validating it in the target system, you can use Custom authentication handles script. To select the script, go to webconsole > Policy > Authentication policy, find Managed system authentication policy that you configured and click Edit icon. The script can be selected in Authentication policy composition options tab in Custom authentication handles script field, as shown below. You can use the default script in /usr/local/openiam/conf/iamscripts/AM/AuthenticationLoginCustomHandler.groovy or amend it to fit your business purpose.
In case you want to switch to Managed System authentication type, it is important to create two Content providers, at least for the trial run. It is of utmost importance since provided the Content provider doesn't work for any reason, having only Content provider for authentication, the system will not authenticate the user.
Whenever you want to configure authentication via other Managed System, create another Content provider, test the authentication type created, while being logged in via old Content provider to be able to log in and out as needed.
As soon as new Content provider works, switch to it and use it for authentication. But we don’t recommend deleting the old Content Provider, as it may cause damage to the system.