Access rights
Access rights in OpenIAM act as tags for user-role, user-group, and user-resource relationships. OpenIAM utilizes access rights as identifiers rather than as restrictive permissions.
Creating Access rights
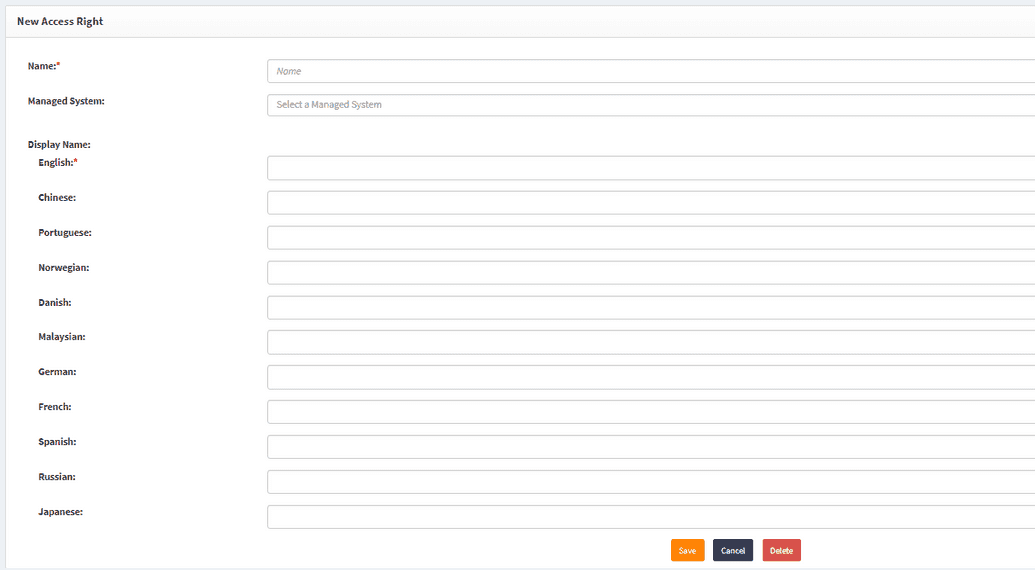
Users can create new access rights and associate them with a Managed System as needed. To do this:
- Navigate to Access Control > Access Rights.
- Click New Access Right in the left-hand menu.
Since access rights are visible in SelfService, localization options are available for their names.
Linking access rights to a Managed system
- Choose a name for the new access right.
- Select a Managed System to associate it with.
- Click Save.
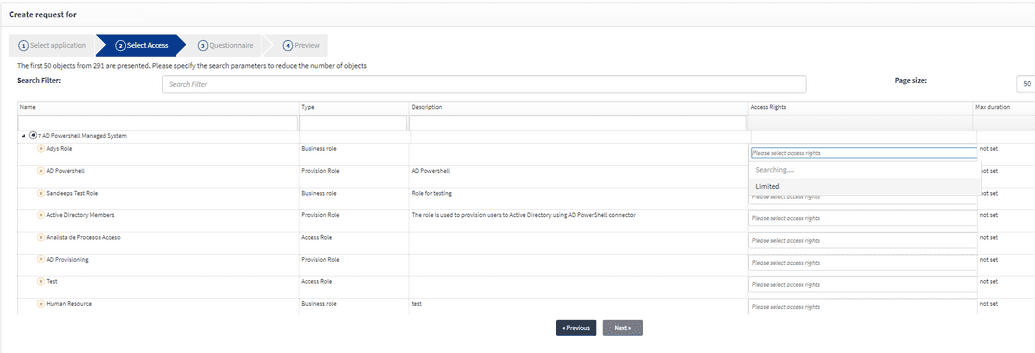
If an access right is linked to a Managed System, it will appear when creating a request:
- Navigate to SelfService > Create Request.
- Select from Service Catalogue.
- Go to Directories and choose your Managed System.
- In the Access Rights column dropdown, the newly created access right will be available.
Access rights that are not linked to a Managed System will not be displayed in this section.
Default access rights
There are three default access rights in OpenIAM:
IsCertified
This access right is required for role or group relationships that participate in Access Certification.
Admin Access & Owner Access rights are visible in the admin or owner attributes for roles, groups, or resources.
- If a user assigns themselves as a Role Owner or Role Admin while editing a role/group/resource, they automatically become a member of that entity.
- This membership applies only within OpenIAM and does not imply admin or owner status in the target system unless explicitly defined in the Policy Map for provisioning.
Hence, Provisioning and Target Systems If a target system supports entitlement tags such as Owner or Admin, and provisioning includes these access rights in the policy map, OpenIAM will grant the same access in the target system.
However, OpenIAM does not automatically duplicate access rights across systems. This must be explicitly configured. Hence, if the target system supports such type of an entitlement (owner, admin) tag and while provisioning the user pushed Access Right in the policy map then having these tags in OpenIAM also means having same access right in the target system. It is important to remember that access rights duplication is not performed automatically.