View direct reports
Overview
By using the View direct reports feature, managers can view a listing of their subordinates and perform multiple operations on their behalf as described in this document. Instructions on performing operations specific to contractors are also covered below.
- Select User Access > View Direct Reports.
From this screen, a detailed view of subordinates that includes user information and status is nested under the manager’s name. The table below provides an explanation of the column values.
| Column name | Description |
|---|---|
| Name | The name of the user. Collapsible lists for active and terminated subordinates are listed under the manager’s name. |
| Principal | The OpenIAM system account name for the user. |
| Employee ID | The employee ID of the user. |
| Email address | The email address of the user. |
| Phone | The primary phone number of the user. |
| User type | User types are customized by the organization and can contain values such as Employee and Contractor. |
| User status | The status of the user such as ACTIVE, INACTIVE, TERMINATED, etc. |
| Account status | A status of ENABLED means the user can log into OpenIAM and their managed system identities are enabled. A status of DISABLED means the user cannot log in to OpenIAM and their managed system identities are disabled. |
| Start date | The day the user begins their job at the company. |
| End date | The user’s last day at the company. |
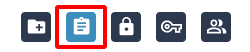
| Actions | The operations managers can perform on behalf of their subordinates. These are described below. |
Active and terminated users
Under the manager’s name on the direct reports screen are collapsible lists organizing subordinates by active and terminated status.
- Log in to the webconsole. Select Administration > System Configuration.
- Go to the Systems tab and select the checkbox for Forbid SelfService operations on terminated users.
- Select Save.
By making this setting active:
- The actions buttons are removed for terminated users from the UI.
- Terminated users cannot be found from the SelfService search header.
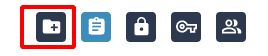
Requesting access
To request additional access for a subordinate, perform the following steps.
- Select the Request Access button for the corresponding subordinate.
- Create a request for the subordinate as documented in the Requesting access via catalog page.
Managers can also request access for themselves from the direct reports screen by following the steps above.
Reviewing access
To review the current access of a subordinate, follow the steps below.
From this screen, the manager can view the current access of the subordinate. Select the Create Access Request button to request additional access for the subordinate. Managers can also review their own access from the direct reports screen by following the step above.
Enabling/disabling user
For managers to use this operation it is imperative they have knowledge of the distinction between a user and an identity in OpenIAM.
This action will toggle the account status of a subordinate. If a subordinate’s account status is enabled, the user's identities in the target systems will be enabled and they will be able to log in to OpenIAM. If a subordinate's account status is disabled, the user's identities in the target systems will be disabled and they will not be able to log in to OpenIAM.
To enable or disable the account status of a subordinate:
- Select the Enable/Disable User button for the corresponding subordinate.

- Enter the reason for enabling or disabling the user in the dialog and select Enable/Disable User.
Resetting password
Managers have the capability of doing password resets for their subordinates. The passwords can be reset for all managed systems the user has identities in or for individual ones.
Given the sensitivity of this operation, managers are required to authenticate themselves using two-factor authentication. This is enabled by following the steps below.
Choose the password change confirmation method:
- Log in to the webconsole. Select Administration > System Configuration.
- Select the Password tab.
- From the field labeled Password change confirmation methods, select Email code, Phone code, or both from the dropdown list.
- Select Save.
Next, enable time-based one-time password (TOTP) in the authentication provider:
- Log in to the webconsole. Select Access Control > Authentication Provider.
- Select Default OpenIAM Auth Policy.
- Select the Supports TOTP Authentication checkbox so that it is enabled. From the field labeled Supported OTP Providers, choose the OTP provider(s) from the dropdown list. The option(s) chosen should support the password change confirmation method chosen above.
- Select Save.
To reset the password of a subordinate:
- Log in to the SelfService portal. Select User Access > View Direct Reports.
- Select the Reset Password button for the corresponding subordinate.

- From the field labeled Select Managed System, select Select all to reset the password in all managed systems the user has identities in, or choose individual managed systems so that the password is only reset in those specific systems.
- Select the TOTP method to receive the code for two-factor authentication. Select Send to receive the code. Note: The code will be sent to the manager, not to the direct report.
- Enter the code in the field labeled Enter Code.
- Enter the new password for the subordinate in the fields labeled Enter Your New Password and Confirm New Password.
- Select Change Password.
Managing identities
For managers to use this operation it is imperative they have knowledge of the distinction between a user and an identity in OpenIAM.
For each subordinate, managers can view a listing of their identities and perform operations such as enable, disable, unlock and view the real-time status of each identity. These operations only affect the status of the selected identity and not the user.
- Select the Manage Identities button for the corresponding subordinate.

- The table below provides a description of each column field in the Manage identities screen.
| Column name | Description |
|---|---|
| User identities | The names of the identities. The search field below the column name allows for a filtered display of results. |
| Managed system | The managed system where the identity resides. The search field below the column name allows for a filtered display of results. |
| Status | The status of the identity. States include ENABLED, DISABLED, or a response from the provisioning connector which indicates the state of the operation. |
| Lock marker | Indicates if the identity has been locked by the managed system due to failed log-in attempts. States include LOCKED or NOT_LOCKED. |
| Create date | The day the identity was created. |
| Last update date | The last day the identity was updated. |
| Actions | Refresh the status of the identity. This is described below. |
Select the checkbox of the corresponding identity to be updated.
- Select the Operation Type from the dropdown list:
- Enable. Selecting this operation will allow the user to access this identity. Note: If after performing this operation the status for the identity is displayed as PENDING_ENABLED, it indicates the provisioning request is waiting to be processed by the connector.
- Disable. Selecting this operation will prevent the user from accessing this identity.
- Unlock. If the user is locked out of this identity due to failed log-in attempts, the operation will allow the manager to unlock the account so that the user may resume access to this identity.
Select Apply.
Note: It is important to understand that if the following occurred in chronological order:- The manager disabled an identity for a subordinate through the Manage identities function.
- The manager later disabled the account status of the subordinate through the Disable user function.
- The manager, at an even later date, enabled the account status for the same subordinate through the enable user function.
Then the identity that was individually disabled in step #1 is not automatically enabled after step #3. Identities that are disabled through the Manage identities function would need to be individually enabled after the subordinate's account status is enabled. The latter is not the only method of enabling the identities in this scenario and that modifications to the provisioning process can automate this task.
Refreshing identity status
For identities that reside in Active Directory, the refreshing action displays the latest change in status for an identity in real-time. This action aids managers who need to see the latest changes in identity and locked/unlocked status.
- Log in to the webconsole. Select Administration > Groovy Manager.
- Enter the following path in the field Select Groovy Script for Loading >
/sync/identities/refreshIdentity.groovy. - Select Load to view the script.
- Upon completing modifications of the script, select Save.
Initiating bulk request
This feature allows managers to request access for multiple direct reports simultaneously.
- Select Initiate Bulk Request from the upper right-hand side of the screen.
- Select the checkboxes of the corresponding subordinates that the entitlements will be requested for. Select Next.
- Create a request for the subordinates as documented in the Request access via catalog page. The preview screen will list the direct reports that access is being requested for.
Contractor operations
There are many instances where contractors for an organization are not managed by the HR system. In these cases, supervisors who have contractors as subordinates can manage them directly using the contractor operations feature from within the SelfService portal.
- Select User Access > View Direct Reports.
- Select
ENABLE CONTRACTOR OPERATIONS. Select the checkbox of the contractor(s) you wish to apply changes to, or SELECT ALL to select all the contractors. Select NEXT. - Select the operation you wish to apply to the contractor(s) from the dropdown list:
- Change last date. From the calendar dropdown labeled Last Date, select the last working day of the contractor(s). Access will be disabled for the contractor(s) on the day following the selected date.
- Change reporting manager. Select the type of supervisor from the dropdown labeled Supervisor Type, and then the supervisor from the dropdown labeled Supervisor. This will change the supervisor of the selected contractor(s).
- Disable. This option disables the access of the selected contractor(s).
- Enable. This option enables the access of the selected contractor(s).
- Add an entitlement. This option grants additional entitlements to the selected contractor(s). Select the type of entitlement(s) from the multi-select list labeled Select entitlement type:
- Group. Select the managed system from the dropdown labeled Group managed system. Select the group(s) from the multi-select list labeled Select Groups.
- Role. Select the managed system from the dropdown labeled Role managed system. Select the role(s) from the multi-select list labeled Select Roles.
- Organization. Select the type of organization from the dropdown labeled Organization Type. Select the organization(s) from the multi-select list labeled Organization.
- Resource. Select the type of resource from the dropdown labeled Resource Type. Select the resource(s) from the multi-select list labeled Resources.
- Remove an entitlement. This option removes entitlements from the selected contractor(s). To select the entitlements to be removed, please follow the steps described above under Add an entitlement.
Select NEXT.
- Review the contractor operations and select SUBMIT to apply the changes. Select BACK to edit the selected changes or select CANCEL to cancel the operations.