Criipto Authentication
If you need to configure authentication via Criipto, follow the guidelines below.
Configure Authentication
- Log in to the Criipto dashboard.
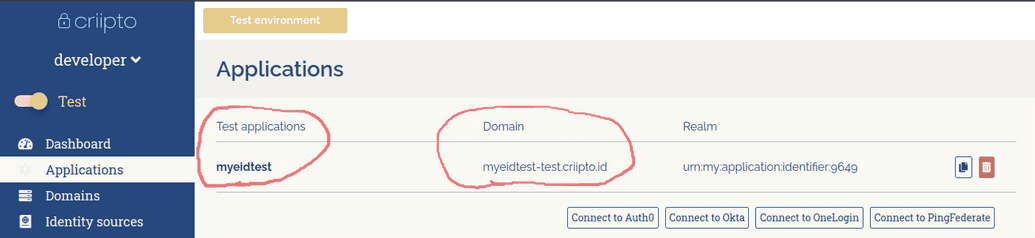
- Create an application and domain on the Criipto dashboard as shown below:
More information on this step can be found in the Criipto documentation portal at Criipto Documentation.
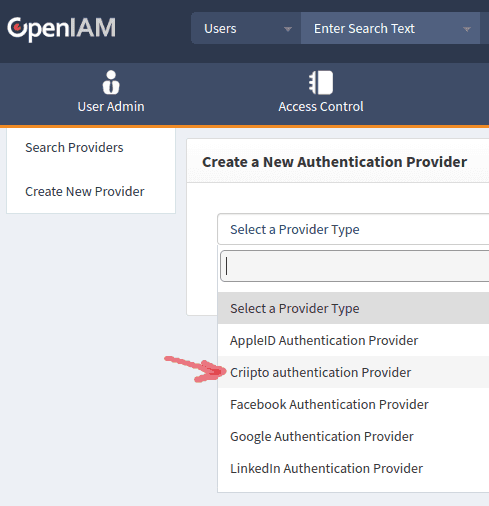
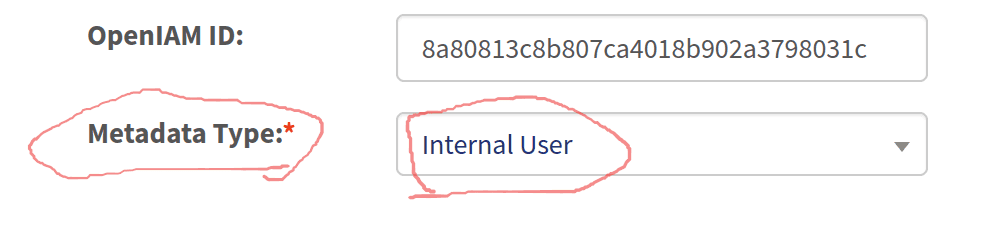
- Create a new authentication provider with the Criipto authentication provider type via the OpenIAM web console.
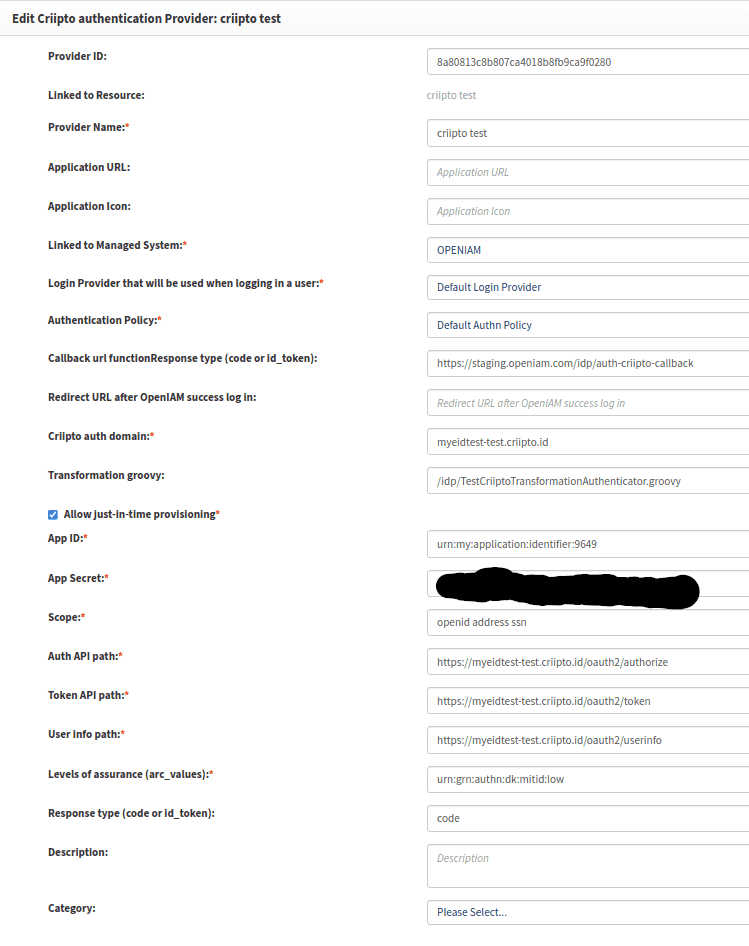
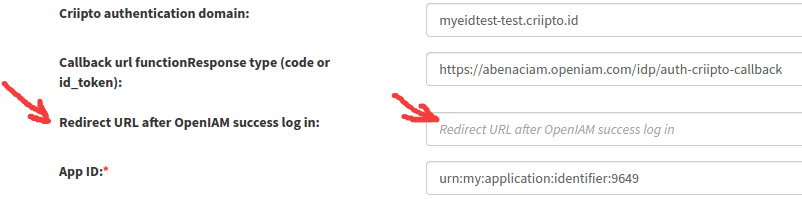
Set the Criipto authentication domain field from step 2.
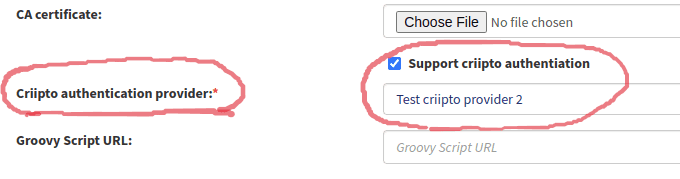
- Set the checkbox and the Criipto authentication provider field on the used authentication provider page.
Use the correct authentication rules for the required URLs. You need to use the default Criipto authentication rule or any custom rule with the Criipto authentication provider. Also, you can set the authentication rule for the Content provider or the required URI pattern.
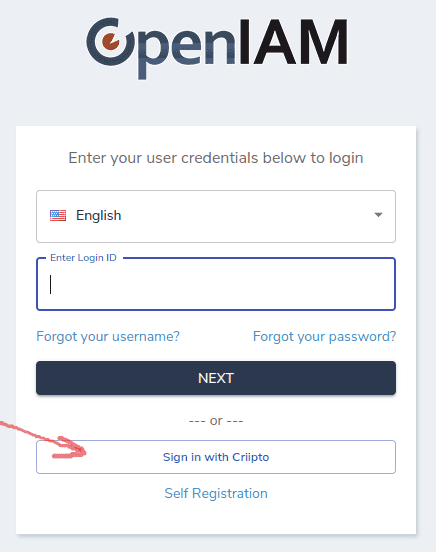
Log in with Criipto from the login page.
It will redirect you to Criipto Login.
- After a successful login, you will be redirected to /selfservice or the predefined URL. This URL must be set on the Authentication provider page for the Criipto authentication type.
You can use the following URL: https://abenaciam.openiam.com/idp/auth-criipto?direct=true to go to step 6.
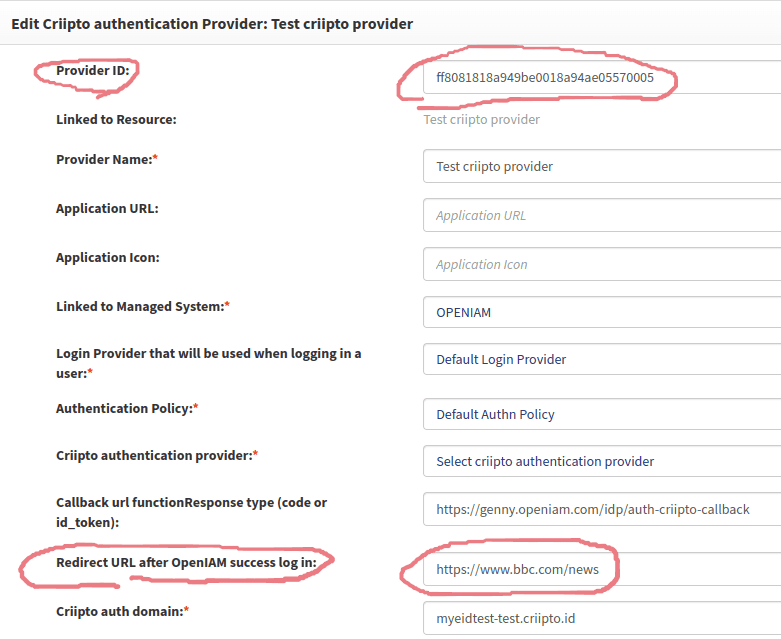
Select a Criipto authentication provider by Criipto login GET request. If you have several Criipto authentication provider configurations, you can select it by a GET request. For example: https://test.domain.com/idp/auth-criipto?direct=true&authProviderId=ff8081818a949be0018a94ae05570005
In this case, on Criipto authentication, the Criipto authentication provider with Provider ID = ff8081818a949be0018a94ae05570005 will be used.
If you need several different redirect URLs, you can create several Criipto authentication providers with equal domains, secrets, etc., but with different “Provider ID” and “Redirect URL after OpenIAM success log in”.
You will call GET request with the required authProviderId and get redirected to the required URL: From the screen above:
GET call: https://test.domain.com/idp/auth-criipto?direct=true&authProviderId=ff8081818a949be0018a94ae05570005
Redirect URL: https://www.bbc.com/news
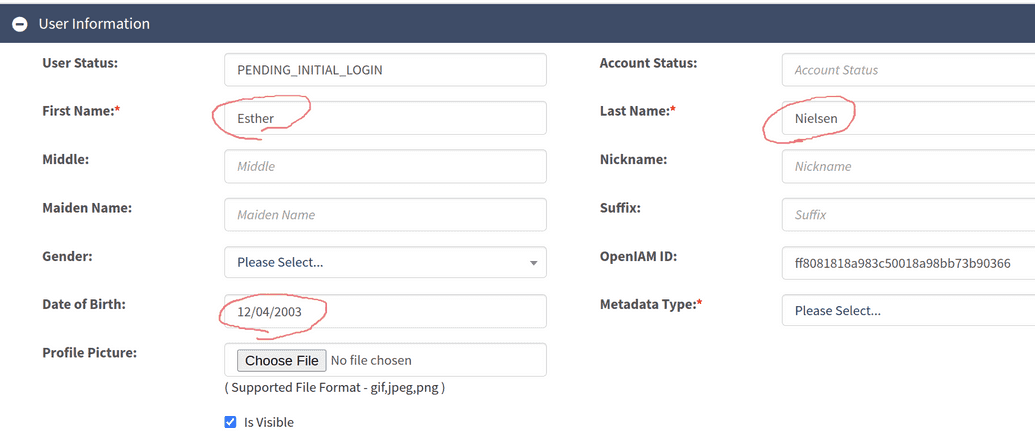
- After the first login, you need to create a user in OpenIAM.
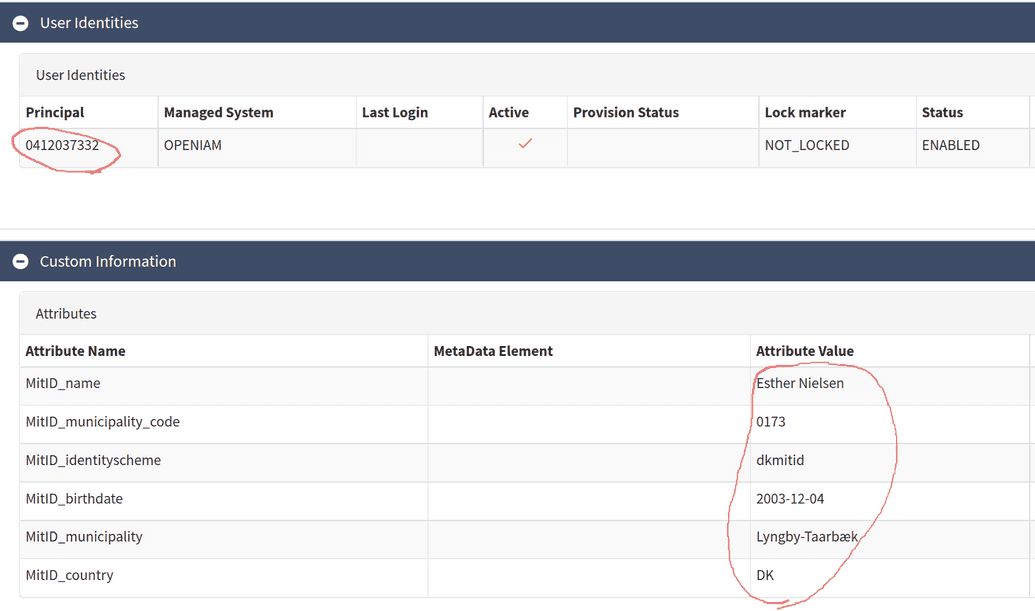
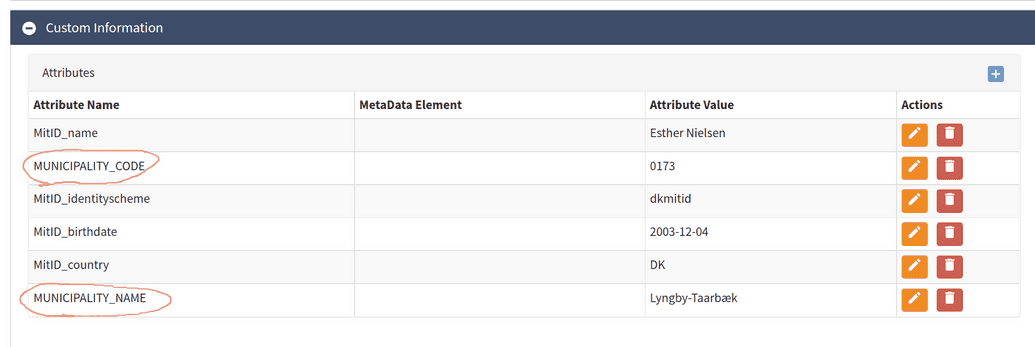
If a user doesn't exist in OpenIAM, you can create a user and log in. User data from Criipto:
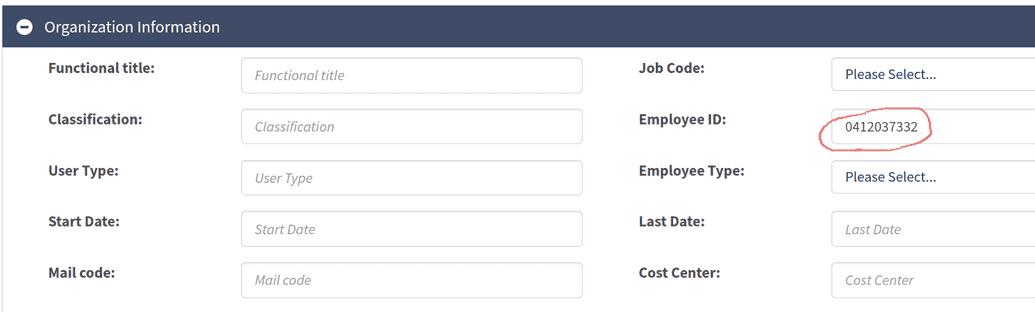
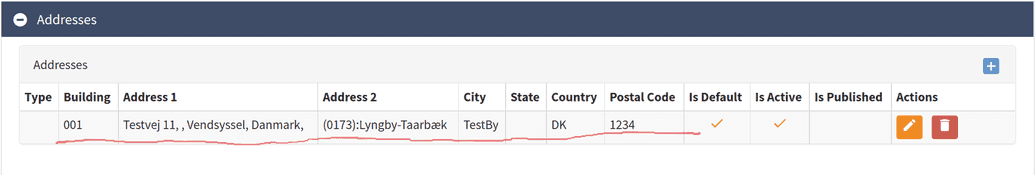
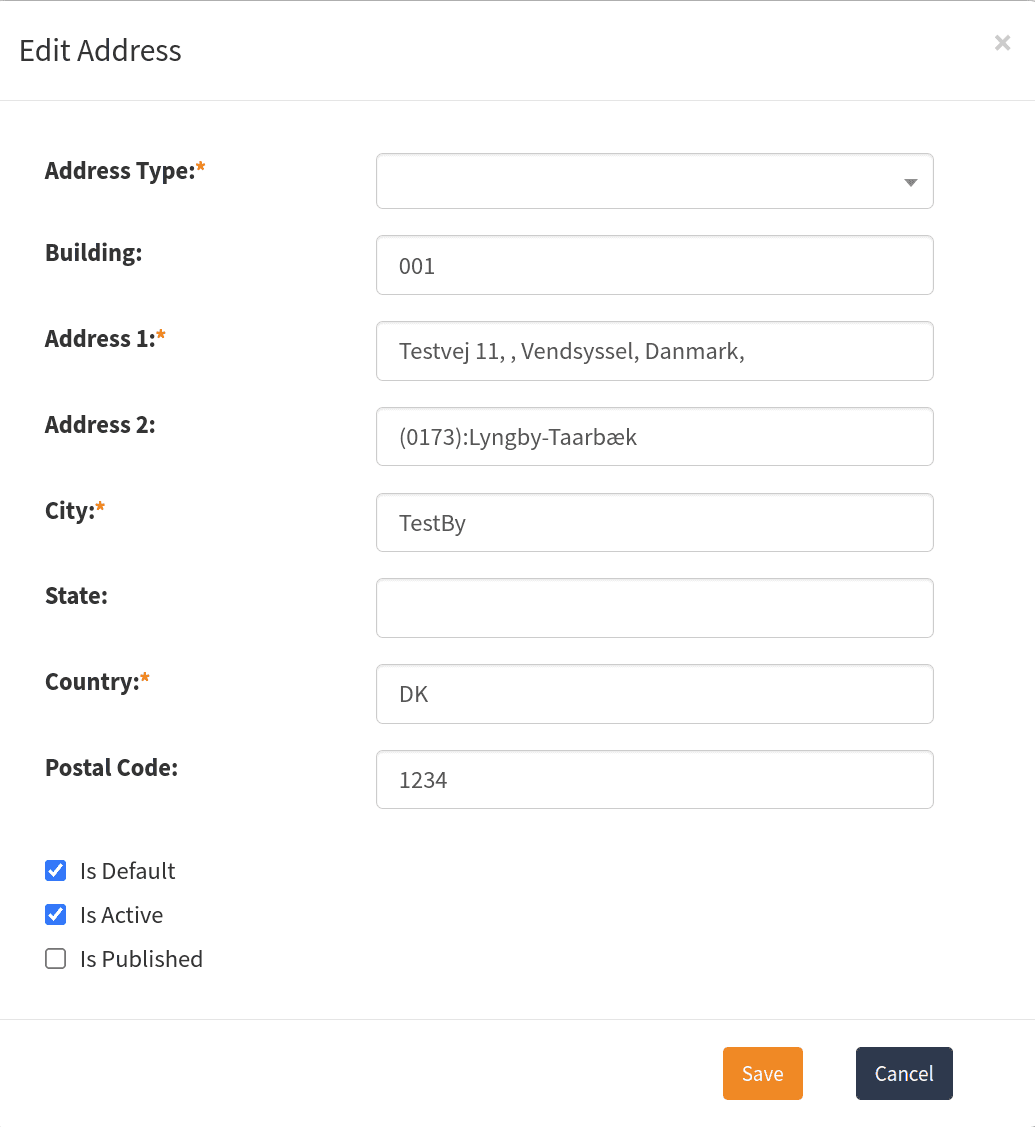
User data saved in OpenIAM:
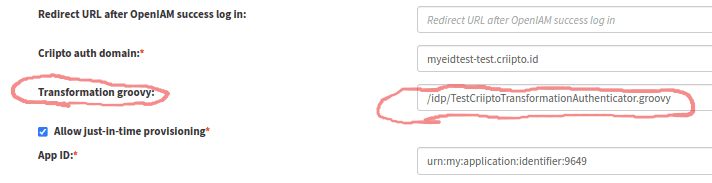
- For customization of user data on JIT provision, you can use a Groovy script. This script can be set on the Authentication provider page.
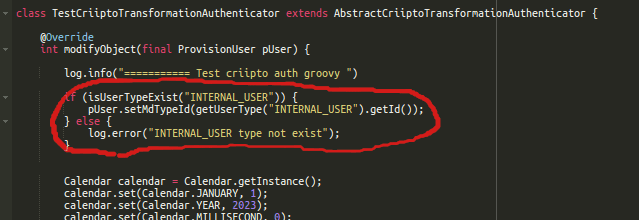
A default Groovy script can set the user-type and rename required attributes:
Results:
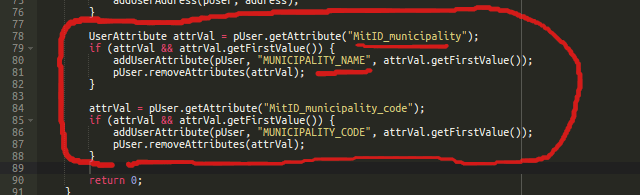
Example Groovy script
// Groovy script code hereimport org.openiam.idm.srvc.continfo.dto.Address;import org.openiam.idm.srvc.continfo.dto.EmailAddress;import org.openiam.idm.srvc.continfo.dto.Phone;import org.openiam.idm.srvc.grp.dto.Group;import org.openiam.idm.srvc.org.dto.Organization;import org.openiam.idm.srvc.res.dto.Resource;import org.openiam.idm.srvc.role.dto.Role;import org.openiam.provision.dto.ProvisionUser;import org.openiam.ui.groovy.criipto.AbstractCriiptoTransformationAuthenticator;import org.openiam.idm.srvc.user.dto.UserAttribute;import java.util.Calendar;class TestCriiptoTransformationAuthenticator extends AbstractCriiptoTransformationAuthenticator {@Overrideint modifyObject(final ProvisionUser pUser) {log.info("=========== Test criipto auth groovy ")if (isUserTypeExist("INTERNAL_USER")) {pUser.setMdTypeId(getUserType("INTERNAL_USER").getId());} else {log.error("INTERNAL_USER type not exist");}Calendar calendar = Calendar.getInstance();calendar.set(Calendar.JANUARY, 1);calendar.set(Calendar.YEAR, 2023);calendar.set(Calendar.MILLISECOND, 0);calendar.set(Calendar.SECOND, 0);calendar.set(Calendar.MINUTE, 0);calendar.set(Calendar.HOUR, 0);Role role = getRoleById("9");if (role != null) {addUserRoleByName(pUser, role.getName(), null, ["IS_CERTIFIED"].toSet(), calendar.getTime(), calendar.getTime(), "Role description");}Group group = getGroupById("SUPER_SEC_ADMIN_GRP");if (group != null) {addUserGroupByName(pUser, group.getName(), null, ["IS_CERTIFIED"].toSet(), calendar.getTime(), calendar.getTime(), "Group description");}Resource resource = getResourceById("0");if (resource != null) {addUserResourceByName(pUser, resource.getName(), ["IS_CERTIFIED"].toSet(), calendar.getTime(), calendar.getTime(), "Role description");}Organization org = getOrganizationById("100");if (org != null) {addUserOrganization(pUser, org.getName(), "ORGANIZATION", ["IS_CERTIFIED"].toSet(), calendar.getTime(), calendar.getTime());}if (isEmailTypeExist("PRIMARY_EMAIL")) {final EmailAddress email = new EmailAddress();email.setEmailAddress("test@email.com");email.setMdTypeId(getEmailType("PRIMARY_EMAIL").getId());addUserEmailAddress(pUser, email);}if (isPhoneTypeExist("OFFICE_PHONE")) {final Phone phone = new Phone();phone.setAreaCd("456");phone.setPhoneNbr("7890");phone.setCountryCd("+123");phone.setMdTypeId(getPhoneType("OFFICE_PHONE").getId());addUserPhone(pUser, phone);}if (isAddressTypeExist("OFFICE_ADDRESS")) {final Address address = new Address();address.setCountry("Country");address.setCity("City");address.setAddress1("Address 1");address.setMdTypeId(getAddressType("OFFICE_ADDRESS").getId());addUserAddress(pUser, address);}UserAttribute attrVal = pUser.getAttribute("MitID_municipality");if (attrVal && attrVal.getFirstValue()) {addUserAttribute(pUser, "MUNICIPALITY_NAME", attrVal.getFirstValue());pUser.removeAttributes(attrVal);}attrVal = pUser.getAttribute("MitID_municipality_code");if (attrVal && attrVal.getFirstValue()) {addUserAttribute(pUser, "MUNICIPALITY_CODE", attrVal.getFirstValue());pUser.removeAttributes(attrVal);}return 0;}}